Cyber Attacks are constantly on the rise and Cyber Criminals are always trying new ways to get access to your data. One of the most common ways is through Social Engineering. Whether it be via an Email or Phone call, Cyber Criminals have learned that the easiest way to infiltrate your network or gain access to your information is by you simply providing them what they need through Social Engineering.
Cyber Criminals will send emails that may look legitimate at a glance, but in fact they are spoofed emails that are designed to gain key information or get you to install malicious software by clicking on a link or opening an attachment.
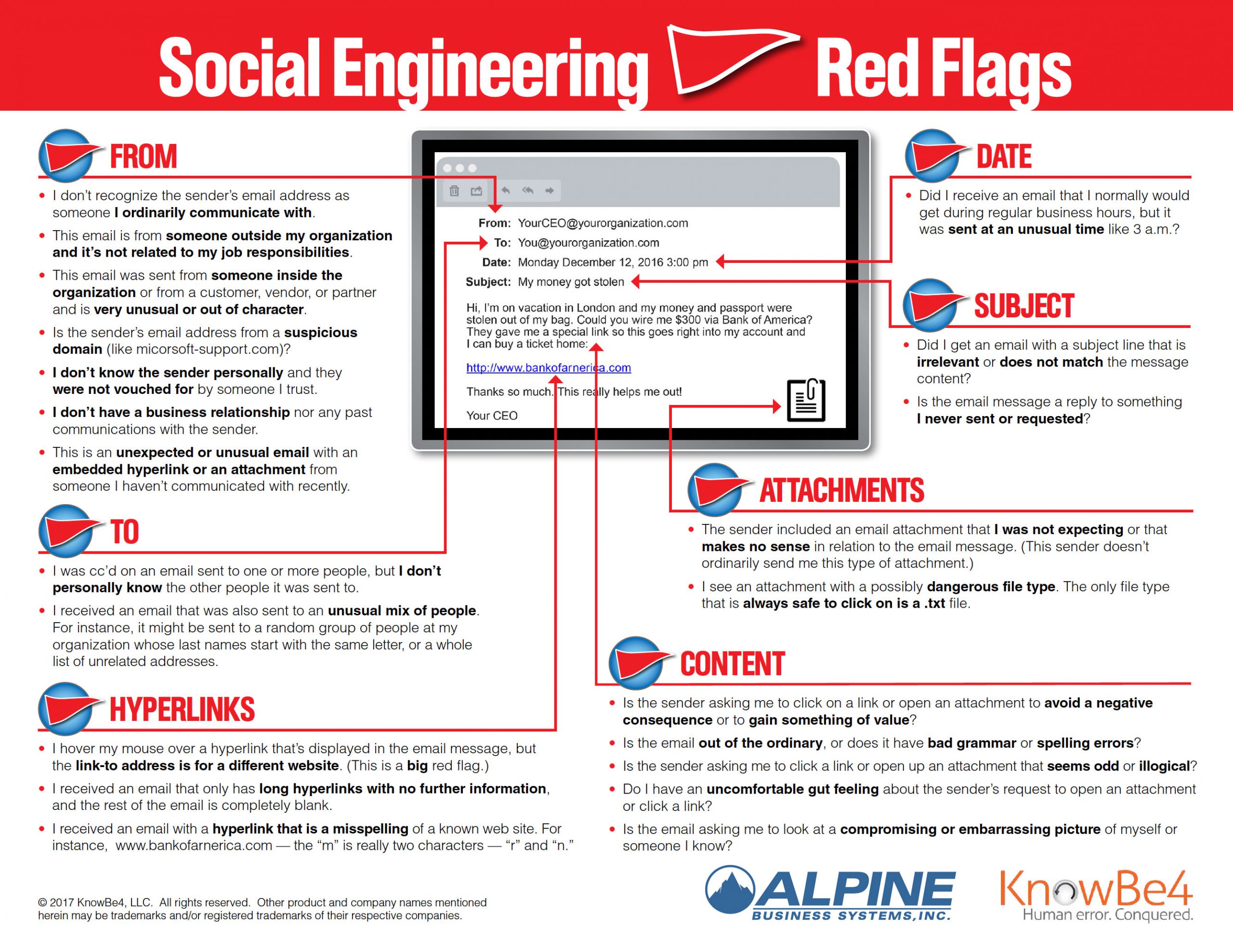
The good news is there are ways to prevent this and below is a list of Red Flags to look out for: